Financial Services
Clarity Over Chaos: How a Fortune 500 Financial Institution Stopped “Panic Patching"
This is the default text value
A leading children's hospital system operates across 50+ locations with over 15k assets. With a lean security team responsible for protecting clinical systems, FDA-regulated devices, and a broad attack surface, the organization needed a way to move beyond raw scanner output and make vulnerability prioritization credible, evidence-backed, and actionable for both remediation teams and executive leadership.
Before Zafran, the hospital's vulnerability management process was driven by legacy scanner reports that were difficult to act on. Remediation teams would push back when handed raw findings, asking which asset was affected rather than taking action. There was no efficient way to cut through the noise and say definitively what needed to be fixed first.
The problem ran deeper than prioritization. The security team had attempted to build an internal dashboard to unify tool data through the API, but the effort was unsuccessful. Without a unified view, there was no reliable way to surface progress to the CISO or upper leadership. Triage was handled spreadsheet by spreadsheet, with limited staff and no mechanism to surface quick wins or track improvement over time.
Healthcare added a layer of complexity that generic vulnerability tools could not address. Many clinical-side endpoints are FDA-regulated and cannot be patched, so the hospital isolated them on network-segmented subnets as a compensating control. But their IoT visibility tool had no awareness of those network boundaries or that isolation was already in place, leaving a gap in how compensating controls were reflected in the overall picture. Without a way to account for those controls, every finding on a regulated device appeared open even when it was already contained.
The hospital implemented Zafran to replace spreadsheet-driven triage with a unified, evidence-backed view of what was actually exploitable across their environment. Legacy scanners, endpoint protection, and network security tools were integrated and actively syncing. Firewall data was ingested via export with an automated collection pipeline in progress, and web application firewall and load balancer data were also brought into scope, giving Zafran the full control context needed to assess true exploitability rather than relying on scanner scores alone.
With live telemetry from endpoint, perimeter, and web application controls, Zafran identified when assets were already protected by active defenses, factoring compensating controls into each vulnerability's applicable exposure score. For FDA-regulated devices sitting on isolated subnets, this meant those findings could be accurately represented as mitigated rather than open, resolving a gap that had persisted before Zafran was deployed.
Ticket volume dropped significantly through Zafran's remediation operations, with a single ticket able to close vulnerabilities across an entire component rather than generating one per finding. ITSM integration let the security team assign tickets to specific teams, set SLA rules by severity, and maintain bidirectional status sync. When sharing findings with server or network teams, direct links to evidence-backed findings removed the ambiguity that had previously generated pushback and delayed remediation.
Executive reporting was a core requirement from the start. The CISO initiated the evaluation specifically for a dashboard that would show exposure reduction trends over time, tying security team effort to measurable progress for leadership rather than a static vulnerability count.
During the initial evaluation alone, Zafran surfaced two findings the team had missed: a resource that had never been decommissioned, and a server that had never been patched, neither of which the legacy scanner had flagged on its own. Across the broader deployment, the hospital:
These outcomes gave the security team a credible, data-driven foundation for prioritization in a constrained healthcare environment, and a clear way to demonstrate exposure reduction progress to executive leadership over time.
Zafran is the only end-to-end AI-native Threat Exposure Management platform that combines continuous vulnerability detection with deep mapping of vulnerabilities to compensating controls to determine what is actually exploitable in your environment.
See why leading enterprises trust Zafran to focus on what actually matters. Discover the new operating model for vulnerability management.

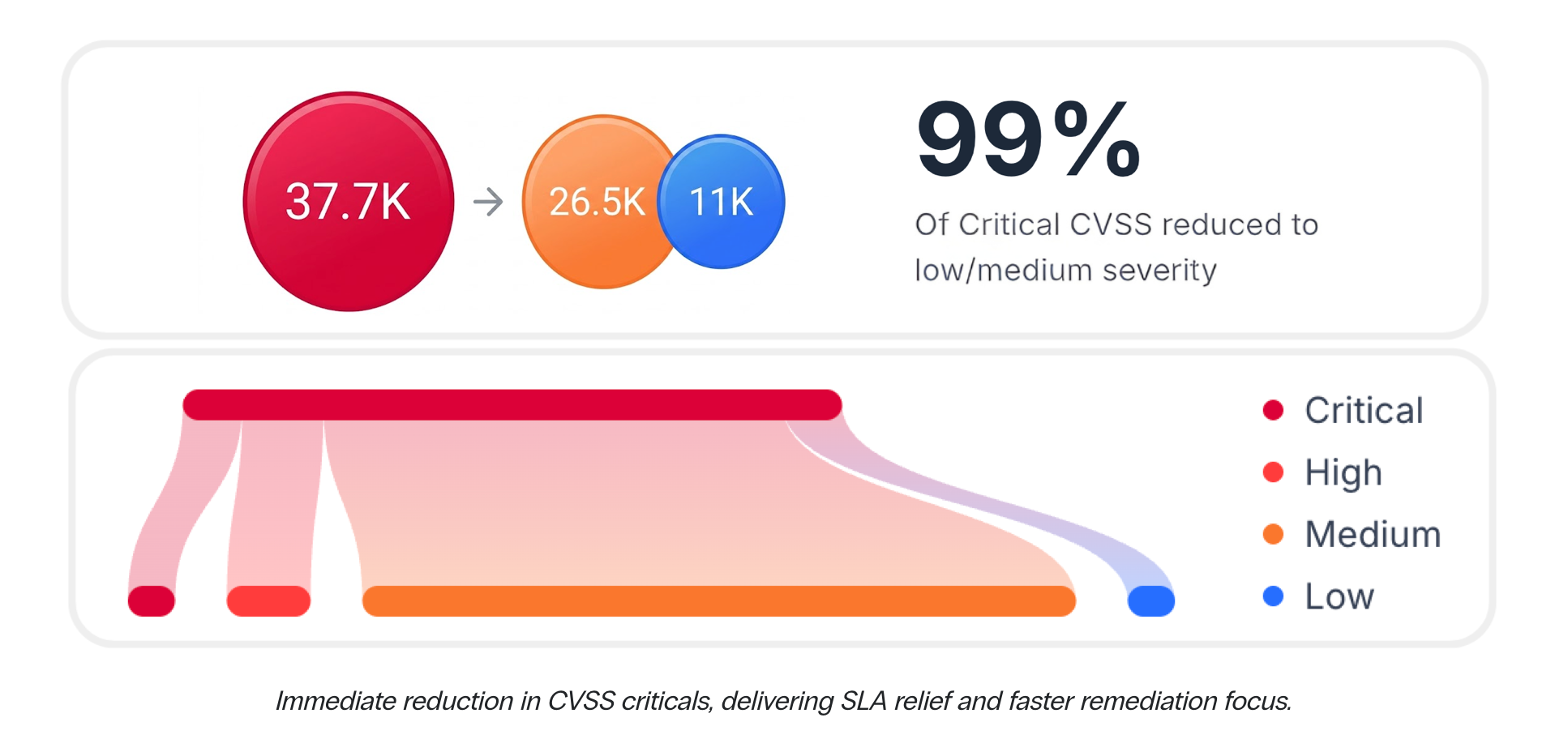
reduction in CVSS Criticals
See Zafran in action
See Zafran in Action
Prioritize and fix what is truly exploitable using risk context from your existing security tools