Blog
Yonatan Keller
NVD Pulls Back on Enrichment: How Defenders Cope With Less Vulnerability Context
April 24, 2026
Agentic exploitation demands agentic response, collapsing the time to neutralize from days to minutes.

Anthropic's Claude Mythos Preview just changed the math on vulnerability risk. It autonomously discovered thousands of zero-days across every major OS and browser, and weaponized known CVEs in under a day, at under $2,000, with no human in the loop. That capability will be in attacker hands within 6 to 12 months.
The volume is rising. The window is shrinking. And the attacks are now machine-speed.
Manual workflows were already falling behind. Keeping pace with this AI-accelerated threat landscape requires a fundamentally different operating model.
The old model is simple: scan on a schedule, produce a list, triage manually, hand off to IT, wait for a patch. Each step is owned by a different team. Each team is working from a different tool. Each tool is seeing a different slice of the environment. Each handoff is creating gaps that widen the exposure window.
The post-Mythos era demands something different. Continuous detection before vulnerabilities are formally named. Exploitability assessment grounded in your actual risk context, not a CVSS score. Automated triage and response that doesn't wait for a human to start the clock.
Imagine starting every day knowing that your environment is scanned for newly disclosed vulnerabilities, assessed and validated in your unique environment, with fixes to the vulnerabilities that actually matter waiting in the ticket queue for the right person.
The Zafran's Zero Day Agent makes that the new normal. It runs continuously across your existing stack, answering the question every team asks when a new zero day drops: Am I exposed? Zero Day Agent detects exploitability within 24 hours of disclosure and automatically routes response to the right people minutes after detection.
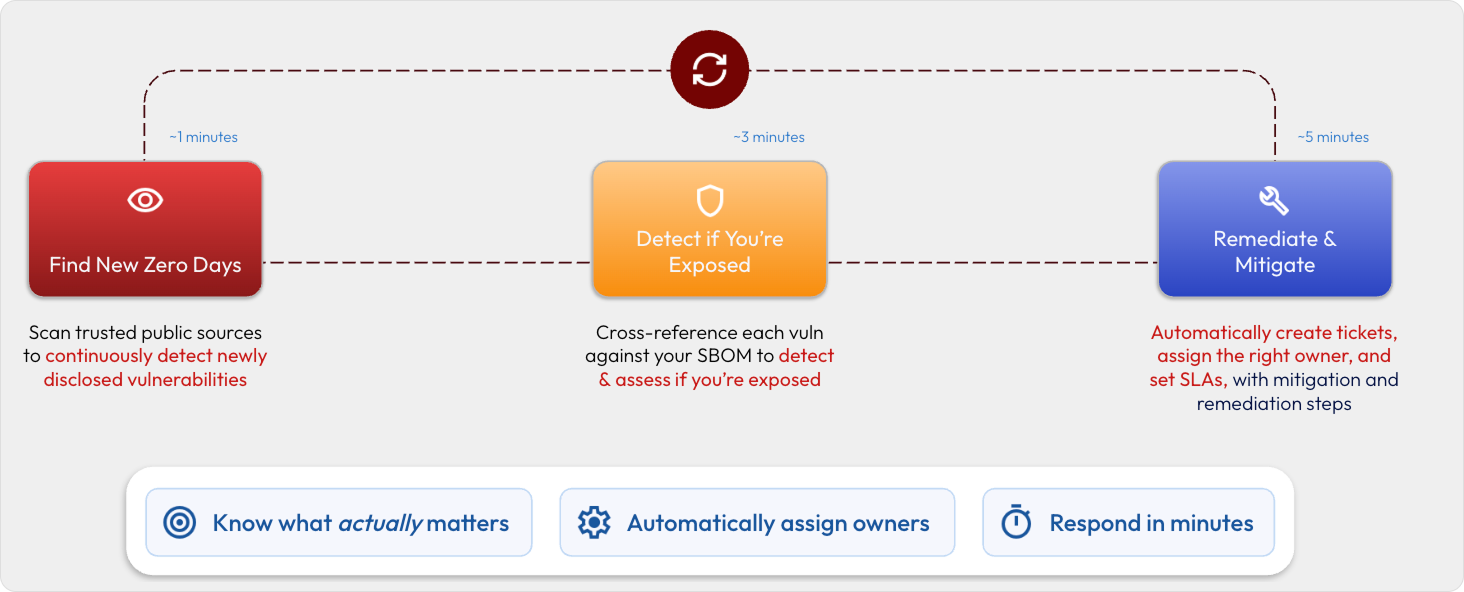
The Zero Day Agent answers a specific problem: how do you respond to newly disclosed vulnerabilities at machine speed. But the deeper challenge facing VM teams isn't any single threat. It's keeping an entire exposure management lifecycle moving at the pace the threat landscape now demands.
Autonomous Workflows are Zafran's answer to that challenge. Complex, multi-step work like detecting exposures, validating exploitability, routing tickets, deploying mitigations, running remediation scripts, and generating reports now happens automatically, with built-in approval flows that keep the right people in the loop before anything executes.
Autonomous Workflows use AI Agents to execute multi-step investigations, generate context-aware reports, and take action across your entire security stack. Simultaneously, Work Item Policies ensure immediate accountability by auto-creating tickets, assigning to the right person, and setting SLAs the moment a vulnerability is detected. Autonomous Workflows eliminate silos, speed up processes, and provide a centralized platform for scalable, repeatable VM playbooks.

Autonomous Workflows takes Zafran's Exposure Management up a notch. Security teams get a solution that scales to match the volume of an AI-accelerated threat landscape, with faster time to respond to the vulnerabilities that actually matter. Not through more headcount, but through automation that runs continuously across the stack your team already owns.
The gap between disclosure and exploitation is measured in hours. The gap between exploitation and response doesn't have to be. The Zero Day Agent and Autonomous Workflows are available now.
Traditional vulnerability management must change. So many are drowning in detections, and still lack insights. The time-to-exploit window sits at 5 days. Implementing a Continuous Threat Exposure Management (CTEM) program is the path forward. Moving from vulnerability management to CTEM doesn't have to be complicated. This guide outlines steps you can take to begin, continue, or refine your CTEM journey.
