Blog
Threat Research Team
Patches take weeks. Exploits take hours. The 2026 DBIR makes the math brutal.
May 20, 2026
The flood of disclosed vulnerabilities will be the largest coordinated disclosure event the industry has ever faced

Yesterday, Anthropic announced Project Glasswing and unveiled Claude Mythos Preview, a frontier AI model that has autonomously discovered thousands of zero-day vulnerabilities in every major operating system and every major web browser. Some of these bugs have been hiding in production code for over two decades.
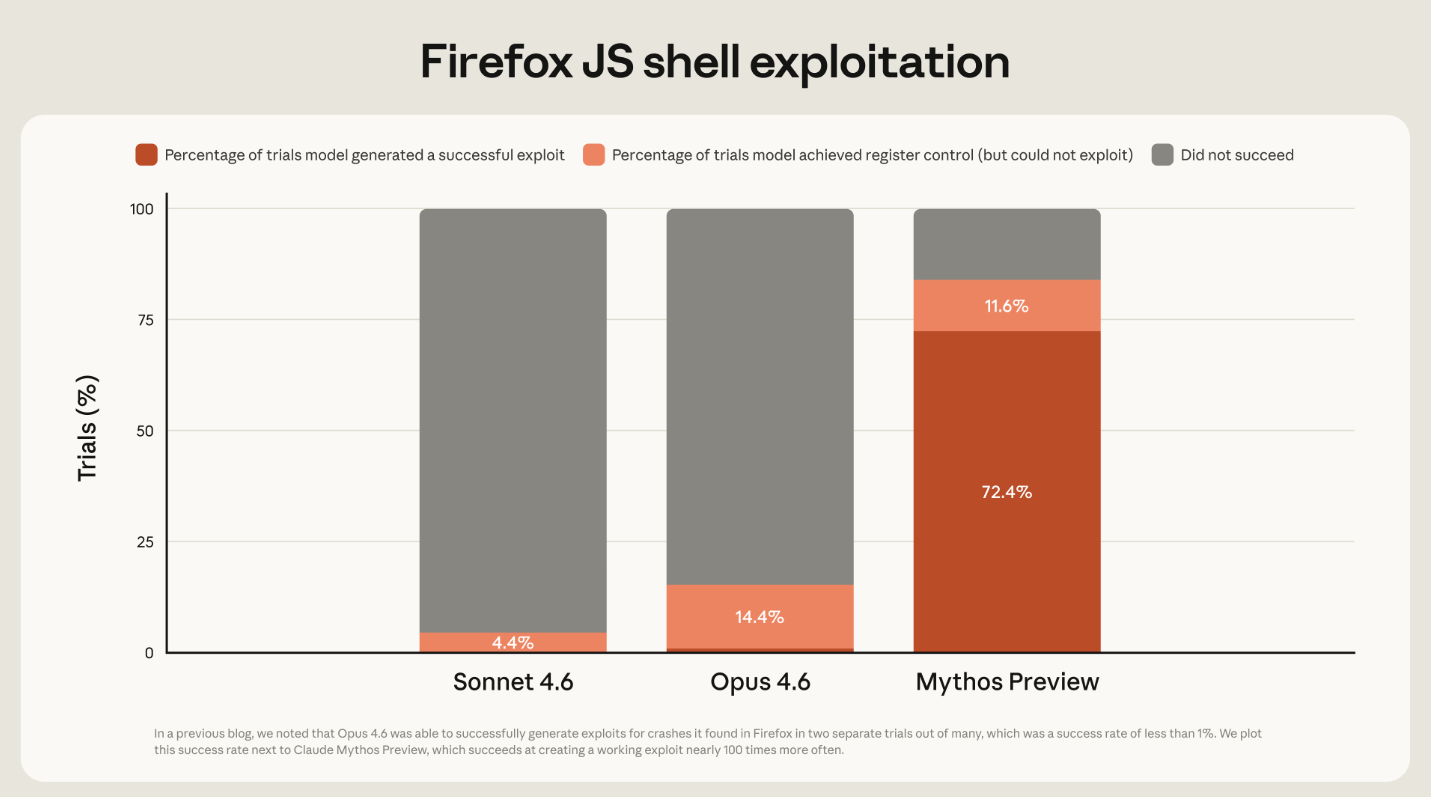
The numbers tell the story clearly. On Firefox JS shell exploitation, Opus 4.6 achieved a 14.4% success rate at generating working exploits. Mythos Preview hits 72.4%. That is a fivefold improvement in a single model generation. And the model didn’t just find surface-level crashes. It chained together four vulnerabilities to build a JIT heap spray that escaped both renderer and OS sandboxes. It found a 27-year-old remote denial-of-service bug in OpenBSD, one of the most security-hardened operating systems in the world. It wrote a full remote code execution exploit on FreeBSD’s NFS server, splitting a 20-gadget ROP chain across multiple packets, completely without human intervention.
We have entered cybersecurity’s Manhattan Project moment. The same capability that lets defenders scan critical codebases and surface vulnerabilities that survived decades of human review also hands attackers an autonomous exploit factory. The power to find and fix is the power to find and weaponize.
The defensive potential is real. Anthropic has committed $100M in usage credits and assembled an impressive coalition: AWS, Google, Apple, Microsoft, CrowdStrike, Palo Alto Networks, the Linux Foundation, and others. They are pointing this capability at the software that underpins global infrastructure. That is the right instinct.
But there is a harder truth underneath the announcement, one that the industry needs to confront directly.
Mythos Preview has already found thousands of critical vulnerabilities. Many of them sit in foundational software: the Linux kernel, major browsers, cryptography libraries, virtual machine monitors. Now consider what happens next.
Anthropic has begun its responsible disclosure process. Patches will flow to upstream maintainers, Linux kernel maintainers first among them. Those patches will become public. And when they do, the vulnerabilities they fix will be visible to every attacker watching the commit logs.
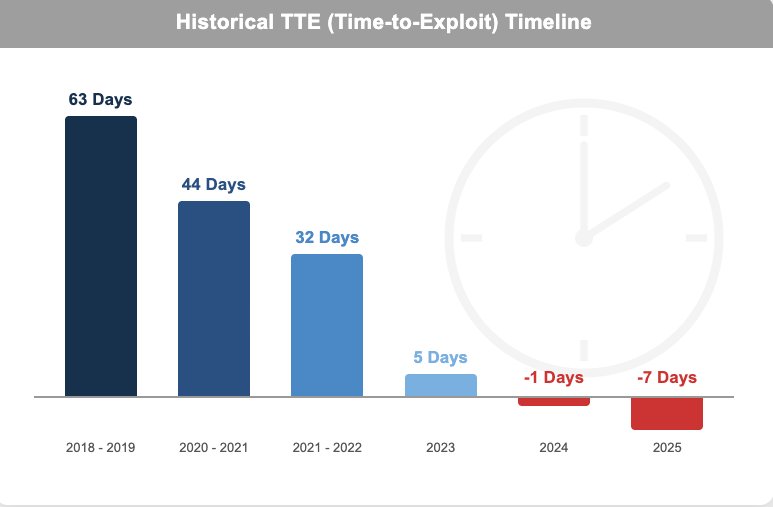
The math here is unforgiving. Writing an exploit from a known vulnerability and its corresponding patch is a largely mechanical process. Anthropic’s own red team blog demonstrates this explicitly: Mythos Preview turned known CVEs into working privilege escalation exploits in under a day, at a cost of under $2,000, with zero human intervention. The window between “patch published” and “exploit available” has collapsed from weeks to hours.
Meanwhile, deploying those patches across enterprise environments takes months. Legacy systems, change management processes, compatibility testing, regulatory review. None of that gets faster because the vulnerability was found by an AI model. The patch-to-deploy gap remains measured in weeks and months while the patch-to-exploit gap is now measured in minutes.
Even keeping the model private does not solve this problem. The vulnerabilities it finds will become public through the patching process itself. Every upstream commit is a signal. Every CVE filing is a roadmap.
The flood of disclosed vulnerabilities will be the largest coordinated disclosure event the industry has ever faced, and enterprises will be left exposed during the gap between disclosure and deployment.
This dynamic is already well-documented. The 2026 Mandiant M-Trends report found that, on average, an exploit becomes available a full week before a patch is even released. That gap existed before AI-driven vulnerability discovery. With Mythos-class models accelerating the rate of disclosure by orders of magnitude, that window will widen, and the consequences will compound.
This is a moment of uncertainty for defenders. The threat is concrete and immediate: AI can now find and exploit vulnerabilities at a scale and speed that the existing security infrastructure was never built to handle. The defensive benefits, while real, will take longer to materialize and require significant changes to how organizations operate.
There is a reason Anthropic brought critical infrastructure organizations into Project Glasswing from the start. They understand that patching alone cannot close the gap. When thousands of critical vulnerabilities are disclosed in a compressed timeframe, the only viable protection during the patch-to-deploy window is compensating controls: network-level blocks, endpoint policies, WAF rules, segmentation changes. Mitigations applied in shift-right, at the point of enforcement, while the organization works through its patching backlog.
Microsoft recognized this problem years ago with MAPP (Microsoft Active Protections Program), which shares vulnerability intelligence with cybersecurity vendors ahead of Patch Tuesday so their products can protect end-users the moment vulnerabilities become public. Anthropic will need a similar approach. Giving defenders access to the model is important, but giving security vendors early access to the vulnerabilities Mythos has discovered, so they can prepare detection signatures and mitigations in advance, is equally critical. Access to the model alone is not enough.
This is the environment we built the Zafran platform for.
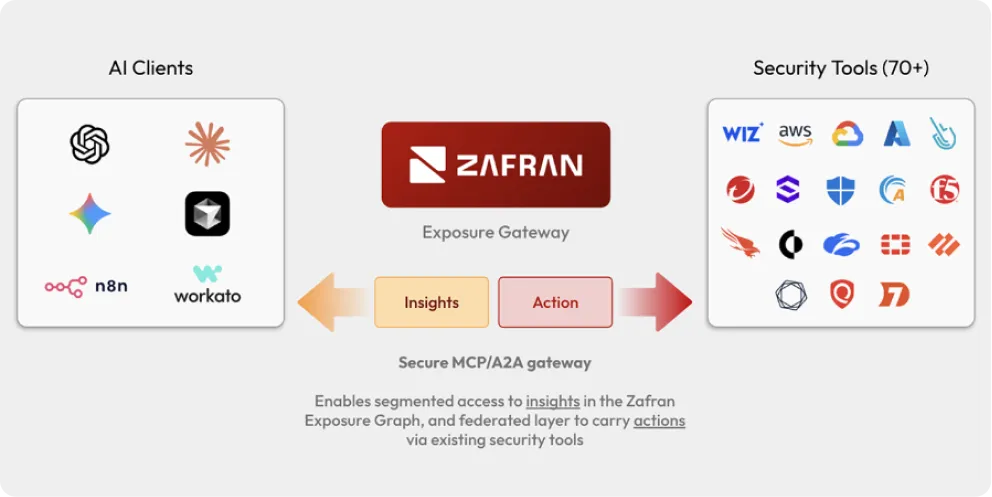
Our Exposure Graph already maps every vulnerability finding to the compensating controls that exist in the environment: network defenses, endpoint protections, cloud-native security tools. When a new CVE drops, the platform can immediately assess which assets are exposed, which are already protected by existing controls, and where gaps remain. That context layer becomes essential when the volume of new disclosures jumps by an order of magnitude.
The Exposure Gateway, the control plane we announced last month, enables AI agents to take autonomous action across the security stack: pushing mitigation rules, opening remediation tickets, deploying patches, all governed by policy and audit controls. When the flood of AI-discovered vulnerabilities arrives, security teams will not be able to triage and respond manually. Agentic remediation, operating on rich exposure context and executing through governed pathways, will be the only way to keep pace.
The sequence matters.
Anthropic has committed to reporting publicly on Project Glasswing’s findings within 90 days and producing recommendations on how security practices should evolve. We welcome that transparency.
But the industry should not wait 90 days to prepare. The first patches are already landing. The disclosure timeline is already running. Organizations should be assessing their mitigation readiness now: identifying their compensating control coverage, stress-testing their ability to deploy emergency mitigations at scale, and building the automation pipelines that will be necessary when the volume of critical findings accelerates.
The Manhattan Project produced a capability that permanently changed the strategic landscape. Project Glasswing has done the same for cybersecurity. The coming months will test defenders in ways they have not been tested before: disclosure volumes will spike, exploit timelines will compress, and security teams will be stretched thin. But on the other side of that transition is a world where critical software has been audited at a depth no human team could achieve, where vulnerabilities that hid for decades have been found and fixed, and where new code ships with far fewer flaws.
AI will find vulnerabilities faster. AI will fix them faster. But the bottleneck was never discovery or remediation alone. It is the ability to deploy fixes into production environments safely, quickly, and at scale. Securely adopting rapid change in production is the most important shift that technology and security leaders need to take on to meet this moment.
Traditional vulnerability management must change. So many are drowning in detections, and still lack insights. The time-to-exploit window sits at 5 days. Implementing a Continuous Threat Exposure Management (CTEM) program is the path forward. Moving from vulnerability management to CTEM doesn't have to be complicated. This guide outlines steps you can take to begin, continue, or refine your CTEM journey.
