Blog
Yonatan Keller
NVD Pulls Back on Enrichment: How Defenders Cope With Less Vulnerability Context
April 24, 2026
A new Gartner report makes something explicit that many security leaders already feel: severity scores alone are failing us.
In "Prioritize What Attackers Will Exploit: 4 Elements of Strong Exposure Prioritization" (Jonathan Nunez, Gartner, March 5, 2026), Gartner lays out the case for prioritization built around how attackers actually behave, not how dangerous a vulnerability looks on paper.
The headline finding:
“by 2028, organizations that prioritize exposures using threat intelligence, asset context, exploitability modeling and security control validation will reduce breach likelihood by at least 70% compared to peers relying primarily on CVSS-based prioritization.”
That's a category-level shift in security outcomes. And it describes exactly what Zafran was built to deliver.
Fewer than 10% of vulnerabilities are ever exploited, yet most programs treat them all as urgent. The result is prioritization paralysis: enormous remediation effort, little measurable risk reduction.
CVSS was designed for a simpler era. Today, threat actors rapidly weaponize a small, specific subset of exposures across cloud, SaaS, identity, and supply chain ecosystems. A severity score that ignores attacker behavior, asset importance, and your deployed defenses isn't just incomplete, it actively misleads prioritization.
Gartner's framework integrates four elements, each addressing a different dimension of risk:
1. Threat Intelligence: Is this exposure relevant to an attacker right now? Threat intel collapses large backlogs by eliminating findings with no evidence of real-world attacker interest, focusing effort on a smaller, genuinely high-risk subset.
2. Asset Context: Would exploitation actually matter? Business criticality, external accessibility, data classification, and privilege relationships determine whether a vulnerability becomes a material risk. Without this, a dev server gets treated the same as a production database.
3. Exploitability Modeling: How likely is exploitation, statistically? Models like EPSS analyze historical exploitation patterns to surface vulnerabilities likely to be weaponized before widespread exploitation is observed; this is the difference between reacting and anticipating.
4. Security Control Validation: Can an attacker actually reach this in your environment? A theoretically exploitable vulnerability may be practically unreachable if compensating controls are properly positioned. Gartner calls this "passive validation," which is also known as confirming exploitability without active testing, in the context of your actual defenses.
Zafran's Exposure Graph maps every asset and vulnerability to the compensating controls deployed in your environment, like your EDR, NGFW, WAF, CNAPP, and more. Not just "is this control present?" but "is it actually blocking this attack path?"
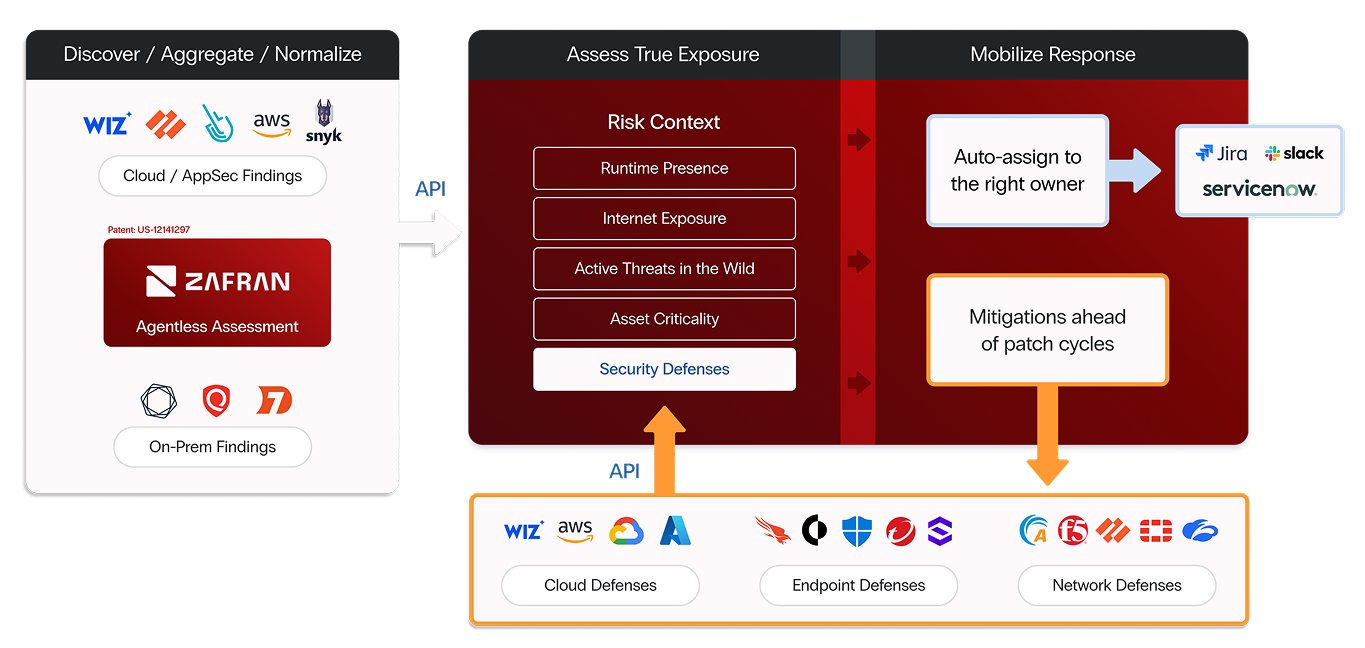
That means Zafran operationalizes all four of Gartner's elements in a single, continuous workflow; Zafran surfaces the small subset of exposures that represent real, material risk, with the context to act immediately using defenses you already own.
Organizations like Summit Utilities have used Zafran to slash "false criticals" by over 90% and dramatically compress MTTR, which is exactly how Gartner says success should be measured: not by vulnerabilities closed, but by reduction in exploitable exposures.
If your program is still anchored to CVSS scores, this report is a useful forcing function. The 70% breach likelihood reduction figure is the kind of number that lands in a board presentation.
Want to see this live? Request a Demo by clicking here
*Gartner, "Prioritize What Attackers Will Exploit: 4 Elements of Strong Exposure Prioritization," Jonathan Nunez, 5 March 2026, ID G00824375.
GARTNER is a registered trademark of Gartner, Inc. and its affiliates. Gartner does not endorse any vendor, product or service depicted in its research publications. Gartner research publications consist of the opinions of Gartner's research organization and should not be construed as statements of fact.
Traditional vulnerability management must change. So many are drowning in detections, and still lack insights. The time-to-exploit window sits at 5 days. Implementing a Continuous Threat Exposure Management (CTEM) program is the path forward. Moving from vulnerability management to CTEM doesn't have to be complicated. This guide outlines steps you can take to begin, continue, or refine your CTEM journey.
