Blog
Threat Research Team
Patches take weeks. Exploits take hours. The 2026 DBIR makes the math brutal.
May 20, 2026

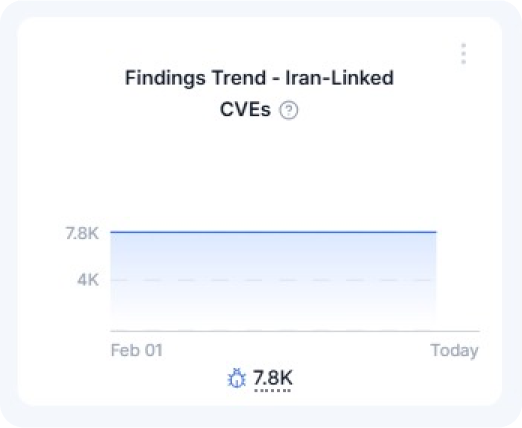
As the Middle East conflict rapidly escalates into a broader regional crisis, Iran’s cyber apparatus has become an active component of the regime’s retaliatory posture, operating alongside conventional military capabilities. This shift follows a prolonged effort to strengthen offensive cyber capacity and transition toward increasingly aggressive operations. In the aftermath of the June 2025 “12 Days War,” Iranian leadership was not deterred; instead, it recalibrated its cyber organizations to function as a dedicated retaliation force in the event of renewed conflict.
In practical terms, since June, Iranian cyber actors have emphasized weaponized data leaks as a strategic tool. Groups such as Handala, linked to the Ministry of Intelligence, have targeted healthcare infrastructure (including the recent Clalit medical data breach) as well as sensitive personal data of political leaders. These operations were not structured as ransomware campaigns and did not involve extortion demands. Their primary objective was psychological impact: to intimidate civilian populations in adversary countries and generate public fear.
At the same time, there has been a notable proliferation of pro-Iranian hacktivist entities since June, including groups such as C.E. Army, DieNet, and Unknowns Cyber Team. While these actors present themselves as independent global hacktivists, evidence suggests they receive funding, tooling, or infrastructure support from Iranian-linked operators, including shared resources and operational coordination.
Long regarded as a strategic instrument of the regime, Iran’s cyber units have, since February 28, aligned closely with the country’s broader wartime doctrine. The pillars of this doctrine are: “punishing” adversaries by significantly targeting civilian infrastructures, expanding Iran’s attack surface to include European and Gulf states, and maintaining strict digital control over domestic opposition. The bottom line: Iranian APT groups are now operating with near-total operational freedom, no longer restrained by the limitations that previously governed their activity.
On the ground, following the launch of the Israeli-American campaign on February 28, numerous Iranian-linked groups have issued unverified claims of successful cyber operations: Handala claimed to have hacked Jordanian gas stations; the so-called Cyber Islamic Resistance asserted it compromised Israeli air defense systems; and other actors reported disruptions to manufacturing and energy distribution networks.
While many of these claims likely serve propaganda purposes and may be exaggerated or false, there is still credible evidence of increased operational activity: an online campaign bringing together known actors - including Handala, the recently emerged Sicarii ransomware group, and the HydraC2 DDoS botnet - has initiated reconnaissance activity consistent with early-stage DDoS preparation; well-known Iranian APTs such as MuddyWater and APT33 are reportedly retooling and scanning critical infrastructure in the energy, water, and financial sectors; and the Fatimiyoun Electronic Team, affiliated with Afghan militia networks and reportedly operating under the guidance of IRGC Quds Force Unit 10,000, has been observed attempting to deploy wiper malware against Western financial and energy organizations.
At a tactical level, Iranian actors have recently been observed using Starlink IP ranges and compromised Israeli commercial VPN infrastructure to conduct vulnerability scanning against critical sectors, including energy and defense. This does not represent a fundamental shift in modus operandi; rather, it reflects infrastructure adaptation designed to obscure traffic origin and bypass IOC-based detection mechanisms ahead of potential escalation.
In any case, we observe that Iranian actors continue to exploit known vulnerabilities rapidly after public disclosure, alongside other methods. In recent years, FortiOS edge-device vulnerabilities were heavily leveraged, and legacy issues such as ProxyShell and Log4Shell remained targets long after patches were available. The state-linked actor Lemon Sandstorm has also extensively exploited edge-device vulnerabilities across platforms including Check Point, Ivanti NetScaler, Palo Alto, and F5 BIG-IP, at times in coordination with major ransomware groups.
Given these developments, U.S. corporations must recognize that they are entering a period of heightened cyber risk. Iranian state-sponsored actors have consistently demonstrated both intent and capability to conduct retaliation through persistent, multi-stage campaigns that establish footholds well before visible disruption occurs. The threat extends beyond data theft or temporary outages to include long-term operational degradation, systemic compromise, and reputational harm.
Traditional perimeter-based defenses are insufficient against an adversary that is adaptive, patient, and willing to exploit any exposed surface. Organizations must adopt a proactive, dynamic defense posture. Modern Continuous Threat Exposure Management (CTEM) platforms such as Zafran are critical in this environment. Zafran enables continuous visibility into exposure to Iranian threat groups, identifies exploitable attack paths, prioritizes remediation based on real-world risk, and integrates with existing security tools to mitigate threats before they materialize.
We also maintain a more detailed threat intelligence brief that includes known threat actor profiles, alias mappings, and current IOCs. Due to the sensitive nature of that material, we're not publishing it openly. If you're looking for a copy of our latest report, email us at yonatan@zafran.io
Mitigation recommendations against the Iranian cyber threats
Traditional vulnerability management must change. So many are drowning in detections, and still lack insights. The time-to-exploit window sits at 5 days. Implementing a Continuous Threat Exposure Management (CTEM) program is the path forward. Moving from vulnerability management to CTEM doesn't have to be complicated. This guide outlines steps you can take to begin, continue, or refine your CTEM journey.
