
Blog
Molly Small
Introducing the Zafran Zero Day Agent: An Autonomous Workflow for the Post-Mythos Era
May 7, 2026
Three shifts every vulnerability management program needs to make now.

On May 11, 2026, the Google Threat Intelligence Group (GTIG) published a report that should reset how every security leader thinks about vulnerability management. For the first time, GTIG identified a threat actor using a zero-day exploit that it assesses with high confidence was developed with AI assistance. The vulnerability, a two-factor authentication bypass in a popular open-source system administration tool, was destined for a mass exploitation operation before GTIG worked with the vendor to disrupt it.
This is the moment the industry has been warning about. It is also the moment that exposes how unprepared most vulnerability management programs are for what comes next.
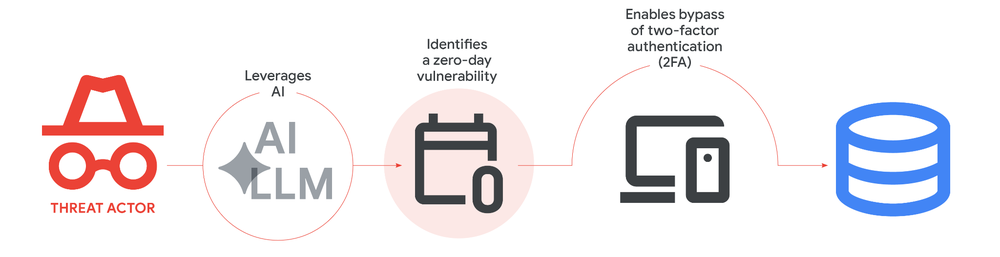
A cybercrime group, working in coordination, used an AI model to discover and weaponize a previously unknown 2FA bypass. The Python script GTIG analyzed carried the unmistakable fingerprints of LLM-generated code: educational docstrings, a hallucinated CVSS score, textbook formatting, and the clean structural patterns that come from training data rather than human authorship.
The vulnerability itself is the part that deserves attention. It was not a memory corruption bug or an input sanitization failure. It was a semantic logic flaw, specifically a hardcoded trust assumption where the developer's 2FA enforcement contradicted its own exception handling. This is precisely the kind of dormant logic error that survives years of human code review and entire generations of static and dynamic analysis tooling.
GTIG's own comparison chart tells the story:

Static analysis tools are blind to these flaws. Dynamic analysis tools are blind to them. Manual expert review catches them, but at human speed and human scale. Frontier LLMs are now effective at finding them, and they operate at machine speed and machine scale.
The category of vulnerabilities that previously required a seasoned auditor with weeks of focused attention is now within reach of any threat actor with API access and a credit card.
The 2FA bypass is the headline, but it sits inside a much larger picture GTIG documented. State-sponsored actors from the PRC and DPRK are using persona-driven jailbreaks and specialized vulnerability datasets to prime models for vulnerability research. APT45 sent thousands of repetitive prompts to recursively analyze CVEs and validate proof-of-concept exploits at a scale that would be impractical without AI assistance. Russia-nexus actors are deploying AI-generated decoy code in malware families like CANFAIL and LONGSTREAM. PROMPTSPY, an Android backdoor, embeds an autonomous agent that queries Gemini to interpret the device screen and execute commands in real time.
The throughline across all of these is acceleration. AI is compressing every stage of the attack lifecycle: reconnaissance, vulnerability discovery, exploit development, evasion, and execution. The disclosure-to-exploitation window has been collapsing for years. AI-assisted exploit development is what closes it for good.

Most vulnerability management programs were designed around assumptions that no longer hold. They assume scanners run on a schedule. They assume CVSS scores correlate with real risk. They assume prioritization can happen manually, ownership can be chased through email, and patch windows can be measured in weeks. They assume that the biggest threats will be the loudest ones.
None of that holds in a world where:
A vulnerability program that produces an unranked backlog of 40,000 annual CVEs and routes them through manual triage was already failing. In the post-Mythos environment, it will be outright dangerous.
A CVE list is not a risk register. What matters is whether a vulnerability is actually exploitable in your environment, on which assets, and what your existing controls already neutralize. Without that context, security teams will spend the AI era triaging findings their own infrastructure has already blocked, while the genuinely exploitable issues sit unaddressed.
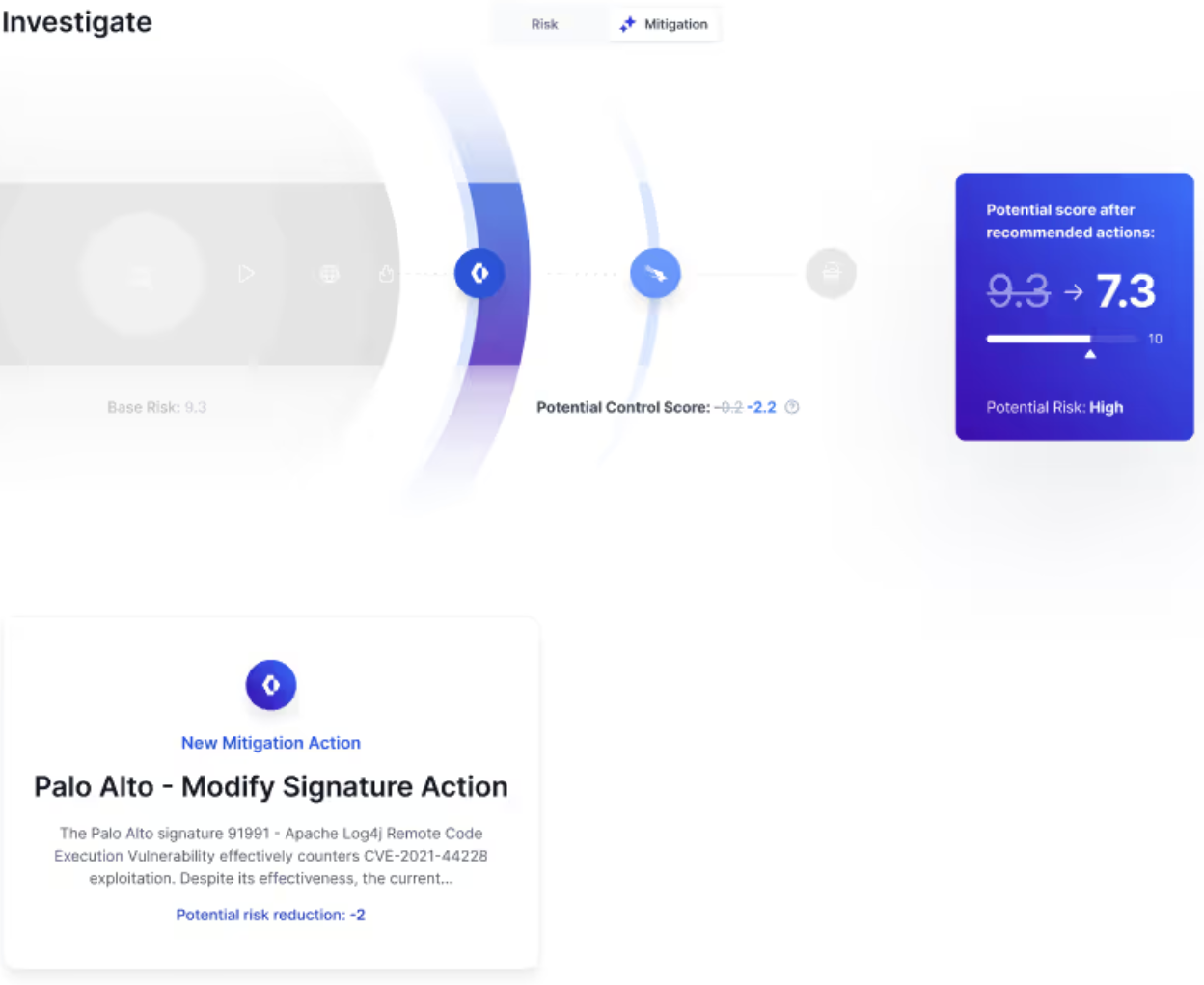
This is the foundation of Zafran's Threat Exposure Management Platform. Zafran continuously ingests findings from across the customer's existing stack of scanners, EDR, CNAPP, and other tools, then applies the Exposure Graph to enrich every finding with runtime presence, internet reachability, threat intelligence, and compensating control coverage. The output is a risk-ordered priority list grounded in what is actually exploitable in the customer's specific environment. For most customers, this reduces critical vulnerabilities by 90 percent.

Patching cannot run faster than AI-assisted exploit development. When the patch-to-exploit gap is measured in hours and the patch-to-deploy gap is measured in weeks, the only viable defense during that window is the security stack the organization already owns: EDR policies, WAF rules, firewall configurations, network segmentation. Knowing what each of those tools is already blocking, and where the gaps remain, is the difference between defensible risk reduction and theater.
Zafran's compensating control mapping is built for this exact problem. The platform identifies which existing defenses already neutralize a given vulnerability and, where gaps remain, deploys compensating controls through the customer's existing EDR, WAF, and firewall tooling. Patches run in parallel. The exposure window closes immediately, using infrastructure the customer has already paid for.
When thousands of AI-discovered vulnerabilities arrive in a compressed disclosure window, no team will triage them by hand. Automation that operates on rich exposure context, with governed pathways for taking action, is the only way to keep pace.
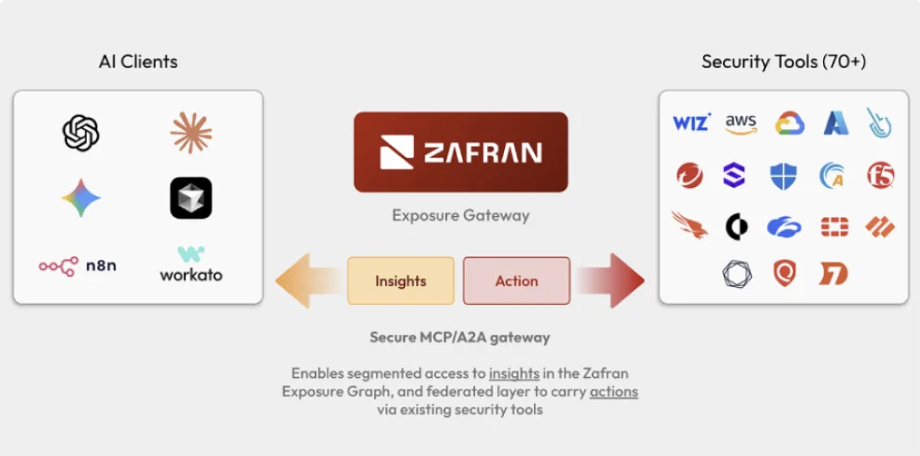
Zafran's Autonomous Workflows address this directly. The Zero Day Agent correlates emerging threat intelligence against SBOM data to identify impacted assets, including for threats without a named CVE. The New CVEs Exposure Agent validates real-world exploitability against runtime state and configuration. Work Item Policies automate ticket creation, owner assignment, and SLA tracking. The agents run continuously, with human-in-the-loop approval on sensitive actions.
And as organizations integrate more AI agents into their security operations, governance becomes the next bottleneck. Zafran's Exposure Gateway is a unified control plane that lets any AI agent, whether homegrown or third-party, to query the Zafran Exposure Graph and execute remediations across the security stack through a single, governed interface. It is the foundation for the autonomous remediation workflows that the AI threat landscape will demand.
GTIG's report documents an active case of AI-assisted vulnerability discovery and weaponization being staged for a planned mass exploitation operation. The window the industry has been told it would have is the window it just used up.
Security leaders should be asking a specific set of questions right now:
If the answers feel uncertain, the time to modernize is now. The threat actors are not waiting.
Traditional vulnerability management must change. So many are drowning in detections, and still lack insights. The time-to-exploit window sits at 5 days. Implementing a Continuous Threat Exposure Management (CTEM) program is the path forward. Moving from vulnerability management to CTEM doesn't have to be complicated. This guide outlines steps you can take to begin, continue, or refine your CTEM journey.
