
This is the default text value
Stop paying for a tool that only produces raw data.
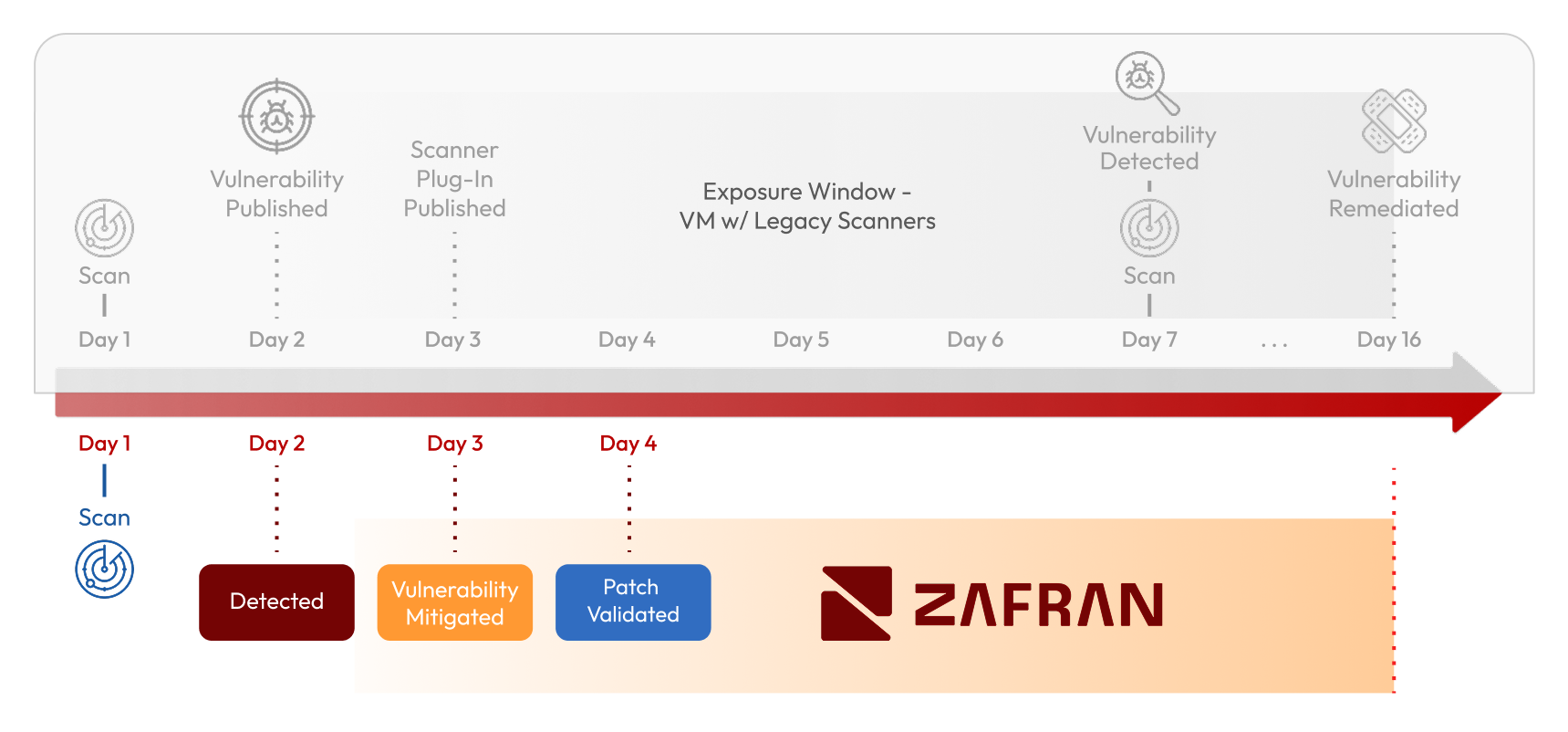
Zafran replaces your legacy scanner with a unified platform that continuously detects vulnerabilities, removes another heavy agent from your stack, and enriches findings with real exposure context so your team can prioritize and remediate what's truly exploitable.
Transform Your VM Program to Deliver True Exposure Management
With Zafran, you can modernize vulnerability discovery while simplifying your security stack:
Continuous vulnerability detection across your environment, combining host detection, network scanning, and external discovery to identify vulnerable assets and services
Immediate risk prioritization, enriching vulnerabilities with runtime presence, internet exposure, asset criticality, and the effectiveness of existing defenses
End-to-end remediation workflows, turning prioritized exposures into clear actions and automatically routing fixes to the right teams to bridge the gap between IT and security
The result is not just a scanner replacement, but a streamlined platform that helps security teams move from vulnerability detection to real reduction of true exposures
4 Weeks to a Smarter VM Program
Connect Existing Security Controls
Enable Zafran Discover
Operationalize Exposure Management
Legacy Scanner Decommission
Connect Existing Security Controls
Enable Zafran Discover
Operationalize Exposure Management
Legacy Scanner Decommission
See Zafran in Action
Prioritize and fix what is truly exploitable using risk context from your existing security tools
