
Blog
Ben Seri
After Mythos: Preparing for Cybersecurity’s Manhattan Project Moment
April 8, 2026

Gartner's latest research surveyed nearly 150 startups building preemptive exposure management technologies. The report segments the market into four categories, and most vendors fall into one: they discover, or they validate, or they remediate. Zafran was recognized as a top-funded Unified Exposure Management Platform (UEMP), and is the only vendor that delivers the complete lifecycle natively in a single platform: discovery, aggregation, prioritization, validation, and autonomous action.
As Gartner noted,
"Zafran drives autonomous neutralization by automatically pushing mitigation policies to existing security controls, defusing threats before exploitation, and provides AI-powered remediation plans to automate fix workflows."¹
Building on that foundation, our recently launched Agentic Exposure Management capabilities deploy autonomous AI agents that detect zero-days before scanners catch up, validate exploitability in real time, and push mitigations directly to your existing controls, all without manual intervention. Gartner projects UEMPs will represent at least half the exposure management market by 2028. This is where the industry is headed, and Zafran is already there.
Every CISO we talk to describes the same frustration. Their teams are buried under thousands of vulnerability findings scattered across dozens of tools. Cloud scanners, identity providers, endpoint agents, application security platforms: they all generate findings, but none of them talk to each other. The result is a fragmented picture of risk, an overwhelming volume of alerts, and a dangerous gap between knowing about a vulnerability and actually doing something about it.
That gap has real consequences. Attackers are moving faster than ever, accelerated by AI-driven tooling, while security teams remain stuck in manual triage and ticket-routing workflows that were built for a different era. The traditional approach, where a scanner finds a vulnerability, a human triages it, a ticket gets filed, and weeks pass before a fix is applied, cannot keep pace with the speed and complexity of modern attack surfaces.
Gartner’s research confirms this. Investment is shifting decisively toward solutions that close the loop on remediation because passive visibility alone is failing organizations. The market is rewarding platforms that deliver actual risk reduction, not another prioritized list of problems.¹
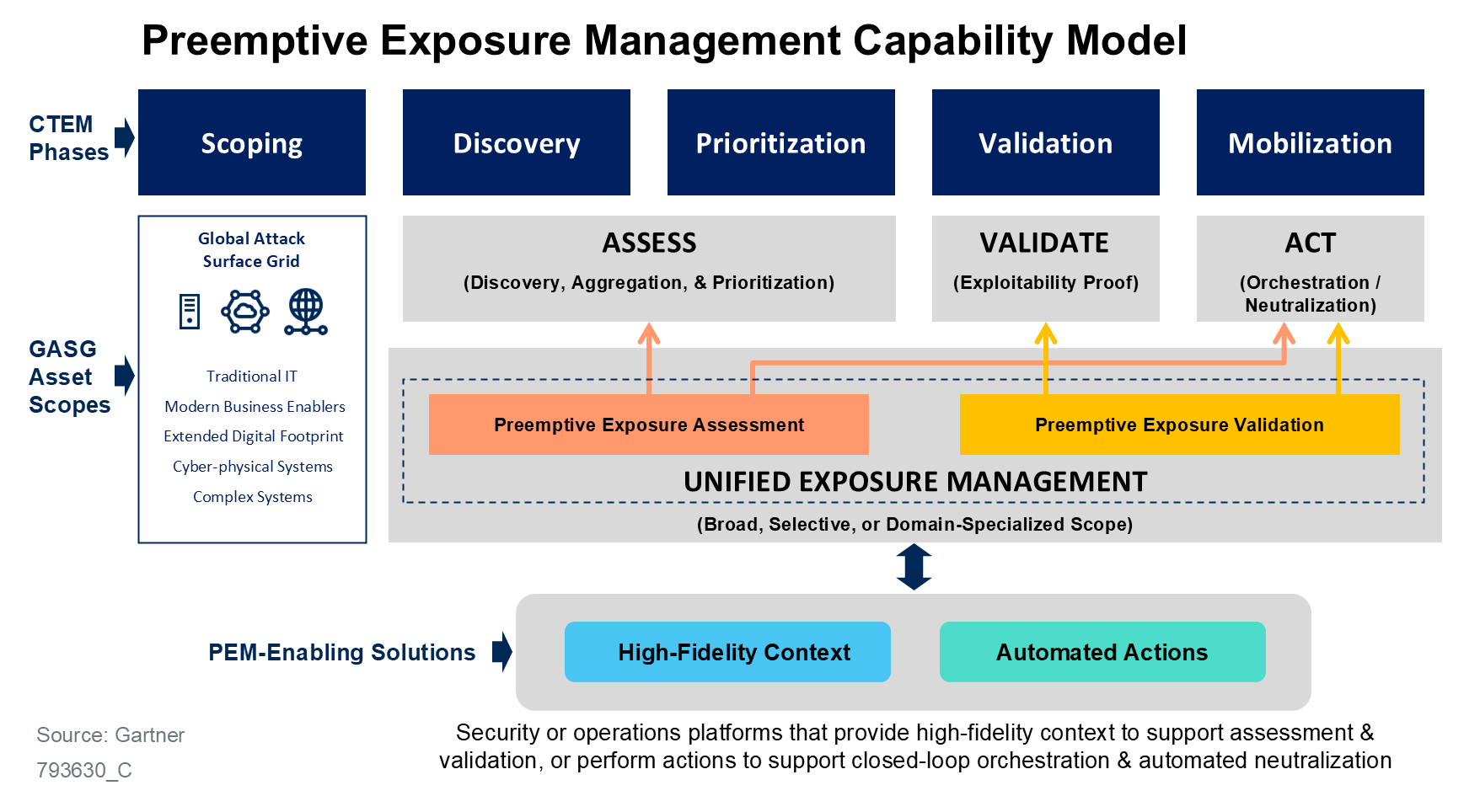
Gartner’s capability model (above) defines the three pillars of preemptive exposure management:
Most vendors in the market address one or two of these pillars. Zafran covers all of them: native discovery, aggregation, prioritization, validation, and action, delivered natively in a single platform.
This Gartner recognition on preemptive exposure management arrives at a critical moment. On April 7, Anthropic announced Claude Mythos Preview, a frontier AI model that autonomously discovered and exploited zero-day vulnerabilities across every major operating system and web browser during testing.² In a separate Gartner analysis of the Mythos announcement, analysts stated that the time between patch and exploit has collapsed, and made the requirements for defending against this new reality explicit:
“This requires effective continuous threat exposure management (CTEM) with discovery of vulnerable code, deep attack path analysis/exploitability, and auto-remediation covering security controls configurations and asset updates. This can’t be a manual process.”
This is the exact architecture Zafran was built around. Of the ~150 startups Gartner analyzed in the exposure management landscape, Zafran is the only vendor that performs deep security control configuration mapping, correlating every vulnerability against the actual state of your deployed cloud, endpoint, and network defenses. That control-aware context is what makes the difference between theoretical risk and validated, exploitable exposure. And it’s what enables Zafran to push autonomous mitigations to those same controls, defusing threats before a patch is even available.
In a world where AI models can reverse-engineer a public patch into a working exploit in minutes, the ability to mitigate ahead of patch cycles isn’t a nice-to-have. It’s the only viable defense.
One of the clearest signals from Gartner’s research is the rapid rise of agentic AI across every category of exposure management. Gartner describes this as a shift toward autonomous systems capable of reasoning and executing complex tasks without human intervention, and identifies it as the defining trend shaping the future of the space.¹
“Agentic AI is rapidly emerging as the new standard for exposure management, as adversaries’ attack speed and the expansion of the global attack surface grid (GASG) increasingly outpace human-driven response time.”
Gartner’s Mythos analysis reinforces this, stating that “security products that only generate alerts or surface vulnerabilities without orchestrating the remediation will rapidly lose market share to platforms that offer complete, agentic workflow automation.”²
Zafran has already shipped this capability. Our Agentic Exposure Management platform deploys autonomous AI agents across the entire vulnerability management lifecycle: detecting zero-days the moment they appear (before scanners catch up), automatically validating exploitability and eliminating false positives, identifying asset owners, and triggering remediation through your existing tools. These agents operate entirely within Zafran’s secure environment, with human-in-the-loop approvals for sensitive actions and full audit logging for compliance.
Gartner projects that by 2030, over 50% of exposure management solutions will natively deliver autonomous validation and mitigation.¹ Zafran is delivering that today.
Gartner segments the market into four technology profiles: Preemptive Exposure Assessment (PEA), Preemptive Exposure Validation (PEV), Unified Exposure Management Platforms (UEMP), and Domain Specialized Exposure Management (DSEM). Zafran sits in the UEMP category, which represents the convergence point where discovery, validation, and action come together in a single platform.¹
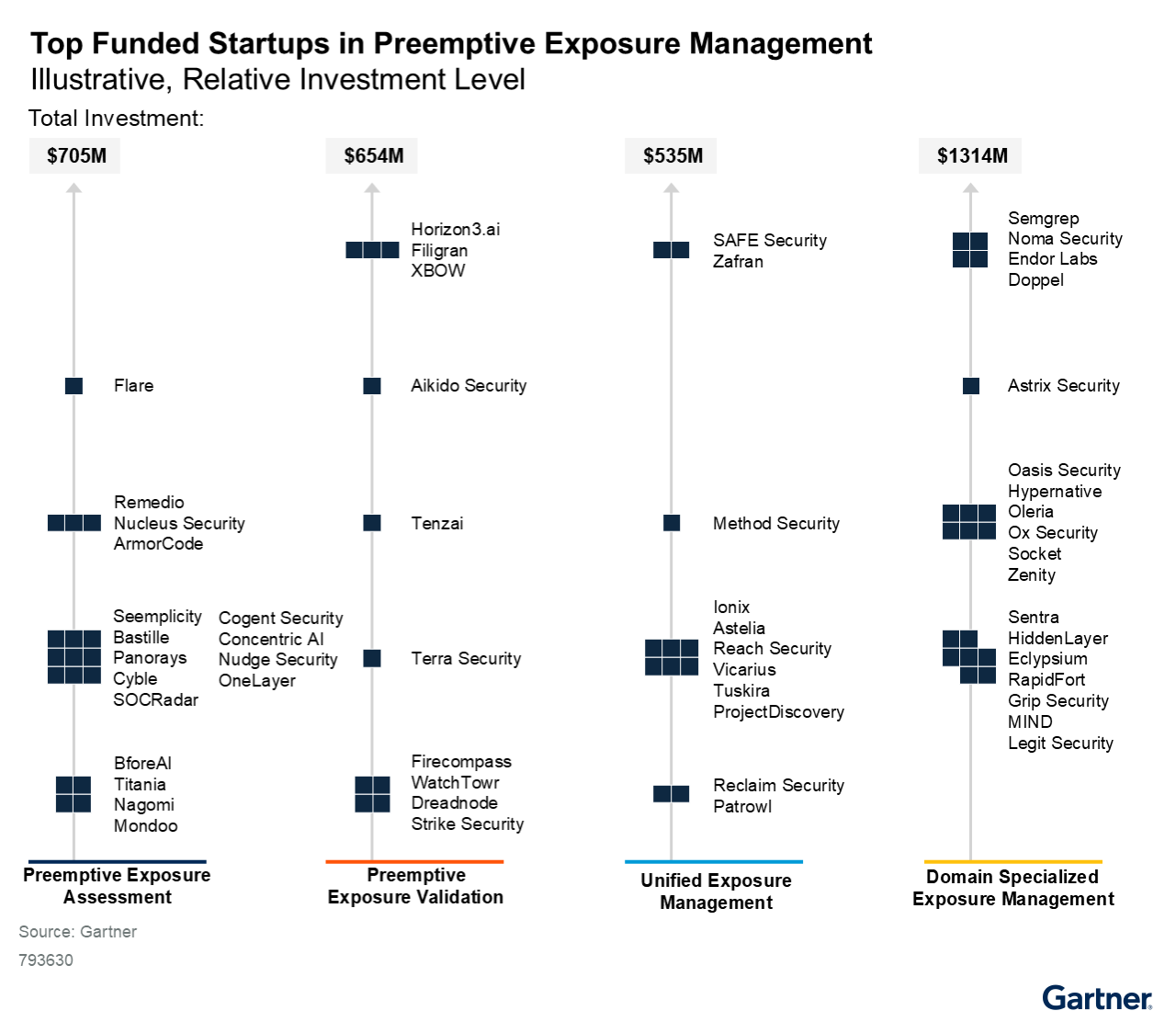
As the figure above shows, Zafran is positioned at the top of the UEMP category. But what separates Zafran from every other vendor in this report, across all four categories, is the completeness of our approach. PEA vendors discover and prioritize but can’t validate. PEV vendors validate but depend on other tools for discovery and action. Domain-specialized vendors go deep in one area but can’t span the enterprise. Zafran delivers all five capabilities natively in one platform: discovery, aggregation, prioritization, validation, and action.
Here’s how that works in practice:
Discover and aggregate. Zafran ingests vulnerability, configuration, and context data from your existing security stack through API-based aggregation, covering cloud, on-premises, identity, and endpoint environments. Our patented Zafran Detector adds native discovery using your existing endpoint agents, with zero additional deployment. The result is a unified exposure graph built from hundreds of data sources.
Assess true exposure. Raw vulnerability counts are noise. Zafran correlates every finding against your actual defensive controls, runtime presence, internet exposure, active threats in the wild, and asset criticality. This deep control configuration mapping is unique to Zafran: we read the actual state of your firewalls, EDR policies, cloud security groups, and WAF rules to determine whether a vulnerability is truly exploitable in your specific environment. This is how we separate the small fraction of exposures that demand immediate action from the vast majority that don’t.
Validate exploitability. Zafran’s exposure graph performs predictive validation by modeling attack chain exploitability against your deployed security controls and risk context. This gives your team definitive confidence that flagged risks are real, which is the prerequisite for authorizing automated remediation.
Mobilize response. Zafran closes the loop in two ways. We drive autonomous neutralization by pushing mitigation policies directly to your existing security controls (cloud, endpoint, and network defenses), defusing threats ahead of patch cycles. And we auto-assign remediation tasks to the right owners through Jira, Slack, and ServiceNow integrations, so the right people are working on the right problems immediately.

The architecture above shows exactly how these capabilities connect. On the left, Zafran aggregates findings from your cloud, AppSec, and on-prem tools while adding native detection through the patented Zafran Detector. In the center, we assess true exposure by layering risk context: runtime presence, internet exposure, active threats, asset criticality, and your security defenses. On the right, we mobilize response by pushing mitigations to your existing controls ahead of patch cycles and auto-assigning remediation to the right owners through the tools your teams already use.
This is a single platform, a single workflow, a single pane of glass. No stitching together three or four different products to cover the full lifecycle. Zafran does it natively.
Gartner’s strategic planning assumptions lay out a trajectory that every security leader should internalize. By 2028, UEMPs are expected to represent at least half of the exposure management market.¹ The organizations that wait to adopt a unified approach will find themselves falling behind adversaries who are already operating at machine speed.
With models like Mythos Preview collapsing the patch-to-exploit window from weeks to minutes, the old playbook of scan, triage, ticket, and wait is a liability. Zafran was built to eliminate that latency by unifying discovery, aggregation, prioritization, validation, and autonomous action into a single platform that works with your existing security investments.
We take an agentless, API-first approach specifically because we know security teams are already managing too many agents and too many tools. Zafran plugs into what you already have, builds a unified exposure graph, and then does the work of actually reducing risk through autonomous policy enforcement and intelligent remediation planning.
This Gartner recognition validates the direction we’ve been building in, and we’re accelerating. We’re deepening our autonomous remediation capabilities, expanding our integration ecosystem, and investing heavily in the agentic AI systems that will define the next generation of exposure management.
For security teams who are tired of drowning in findings with no clear path to action, this is the moment to rethink how exposure management works. The market is consolidating. The technology is maturing. And the threat landscape is not waiting.
¹ Gartner, Emerging Tech: Top Funded Startups for Preemptive Exposure Management, Luis Castillo, Elizabeth Kim, 3 April 2026.
² Gartner, First Take: Claude Mythos Preview and Project Glasswing Push Security Providers to Adopt Autonomous Defense, Mark Wah, Marissa Schmidt, David Senf, Frank Marsala, 8 April 2026.
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved. Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
Traditional vulnerability management must change. So many are drowning in detections, and still lack insights. The time-to-exploit window sits at 5 days. Implementing a Continuous Threat Exposure Management (CTEM) program is the path forward. Moving from vulnerability management to CTEM doesn't have to be complicated. This guide outlines steps you can take to begin, continue, or refine your CTEM journey.
